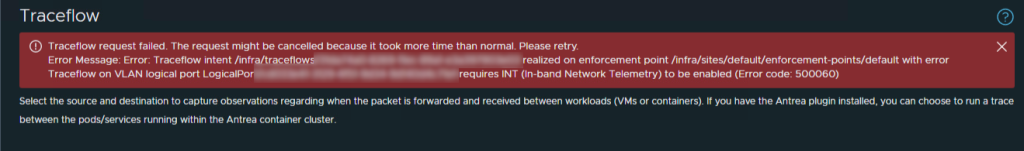
When you try to export an ISO file in VMware vCenter from a cluster using single cluster image with vLCM. You will get the following error:
A general system error occurred: Error occurred while exporting ESXi image and/or image document.The error is accompanied with an error in the vmware-vum-server-#.log file in /var/log/vmware/vmware-updatemgr/vum-server catalog like the following:
2023-06-14T12:21:23.882Z error vmware-vum-server[09453] [Originator@6876 sub=VumVapi::Lib::Utils] [ExportTask 92] Failed to export cluster image from depot. errorCode: 99In my case I was able to export it as a zip bundle and the corresponding json configuration file exported successfully as well.
The problem lies with vendor signatures, and vmware does not currently have a solution for this unfortunately except that it normally helps to remove the vendor packages attached to the cluster.
https://kb.vmware.com/s/article/91237
More information is available here: https://communities.vmware.com/t5/vCenter-Server-Discussions/Cannot-export-vLCM-image-if-you-use-a-custom-SSL-cert-Non/td-p/2881200/page/2